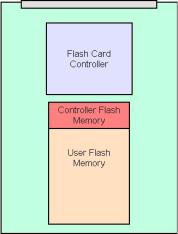
A Flash memory card such as a Compact Flash card is made from two main electrical components:
- A computer chip called the Controller
- Flash Memory
The Flash Memory in the memory card has two main memory sections:
- Flash Memory used by the Controller which is normally not accessible.
- Flash Memory which is accessible to the general user.
The controller Flash memory holds the software program for the Compact Flash controller plus the various tables and values necessary for the CF controller to function correctly.
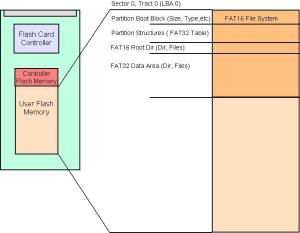
The User Memory is typically formatted into blocks called sectors, which normally have 512 data bytes, so that the CF card can act as a standard computer ATA mass storage device.
When a CF card is first purchased from a CF card supplier, the user Flash memory on the card typically has an empty FAT16 file system referred to as a “Super Floppy File System”. Other file organizations are equally possible and may become highly complex depending upon the actual application the CF is to be used in. A typical new CF card when initially purchased is shown in Figure as below.
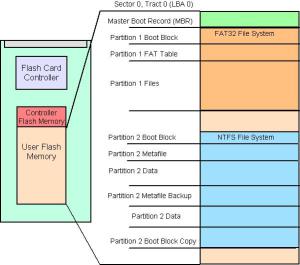
Alternatively, the user memory may have multiple partitions each with its own file system. Each partition may have its own unique organization. The beginning of the user memory normally has a MBR (“Master Boot Record) which contains a table of information on up to four primary partitions. Figure below shows such a possible CF card memory with two partitions containing different file systems (in this example, FAT32 and NTFS).
Normally, the user interested in duplicating CF cards does NOT need to concern himself with the fine points of computer mass storage devices such as MBR’s, partition tables, etc. However, he/she should be aware that following truths apply to all types of duplication.
- A Master Flash card contains a lot more stored information than just the data files that have been stored upon it.
- For correct duplication, special knowledge and care must be taken unless all Target copy cards are exactly the same brand as the Master card and the duplicator makes a complete binary copy of the Master to the Targets which is followed by a complete verification cycle.